Listen to the article
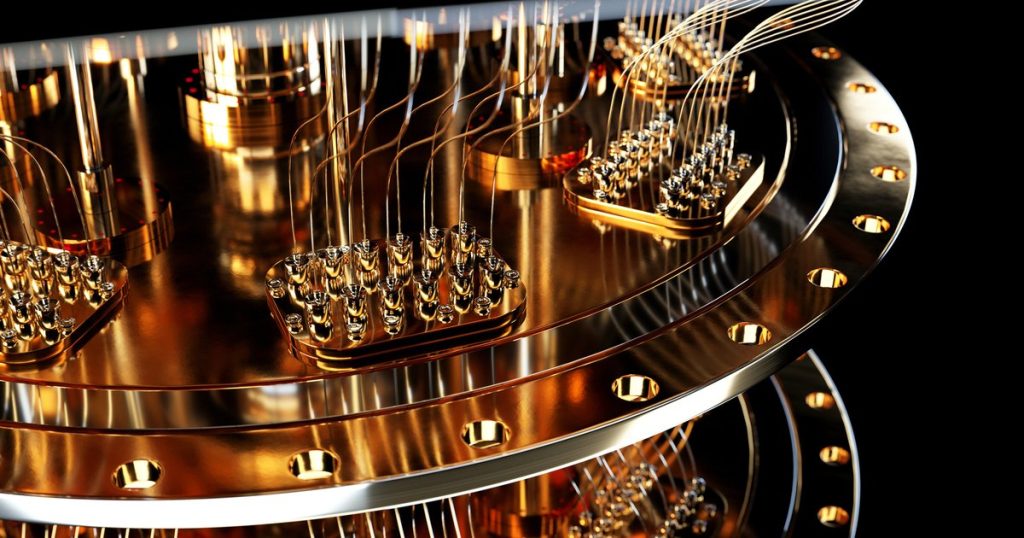
The Quantum Threat Is Real: Why Post-Quantum Cryptography Can’t Wait
Quantum computing poses a more imminent threat to cybersecurity than many realize. While skeptics may dismiss concerns as distant doomsday thinking, cybersecurity experts warn that “Q day” – when quantum computers become powerful enough to break today’s encryption – could arrive as soon as 2030.
More alarmingly, malicious actors aren’t waiting idly for this technology to mature. They’re actively stockpiling encrypted data today, preparing for the moment when quantum capabilities will allow them to unlock these digital treasures. This “harvest now, decrypt later” strategy means organizations face a present danger, not just a future one.
“Even if financial records, health data, intellectual property, or government communications are a few years old when they’re finally decrypted, the damage could be catastrophic,” explains Dr. Andrey Jivsov, a cybersecurity researcher at Quantinuum. “The financial, reputational, and legal consequences remain severe regardless of when the breach occurs.”
Despite the gravity of this threat, many enterprises remain hesitant to implement post-quantum cryptography (PQC), the solution designed to withstand quantum attacks. This reluctance stems largely from misconceptions about PQC implementation.
Debunking PQC Misconceptions
One common misunderstanding is that implementing PQC requires replacing all cryptographic systems. In reality, the transition is far more targeted. Only classical asymmetric algorithms like RSA and ECC, which are vulnerable to quantum attacks through Shor’s algorithm, need replacement.
Modern cryptographic hashing and authenticated encryption methods like AES-GCM remain robust against quantum threats. The vulnerability primarily affects key exchange and digital signatures – two critical functions underpinning modern secure protocols. PQC introduces quantum-safe alternatives such as module lattice-based key encapsulation mechanism (ML-KEM) for key exchange and module lattice-based digital signature algorithm (ML-DSA) for digital signatures.
Another misconception is that PQC requires quantum computers to function. “PQC techniques don’t rely on quantum technology – they’re designed to defend against it,” clarifies Alan Grau, VP of IoT and Embedded Solutions at Sectigo. “These algorithms run efficiently on today’s conventional hardware.”
Some organizations also believe PQC standards aren’t ready for implementation, when in fact standardization efforts are well advanced. The National Institute for Standards and Technology (NIST) in the U.S., along with equivalent agencies in the U.K., Germany, and France, have identified quantum-resistant algorithms following years of global collaboration and rigorous testing.
Simultaneously, the Internet Engineering Task Force (IETF) is finalizing protocol updates that will enable browsers, cloud services, and infrastructure to adopt PQC while maintaining compatibility with existing systems.
The Danger of Inaction
Perhaps the most dangerous misconception is that quantum threats remain purely theoretical or decades away. This complacency ignores the active data harvesting occurring today.
“We can’t predict exactly when quantum computers will reach the scale needed to break encryption – it could be five years or twenty,” says Dr. Michele Mosca, co-founder of the Institute for Quantum Computing. “But considering that much of today’s sensitive data will remain valuable for years, we can’t afford to wait and see.”
The finance, healthcare, and defense sectors face particular risk, as their data retains value for extended periods. Once sensitive information is exposed – whether immediately or years later – the damage becomes irreversible. Privacy breaches and broken trust have lasting consequences that can’t be undone.
Building Quantum Resilience Today
Security experts recommend three immediate steps for organizations to build quantum resilience:
First, monitor key exchange proposals to identify which software components aren’t PQC-ready. This assessment helps prioritize necessary upgrades.
Second, adopt standardized PQC key exchange mechanisms, which are already supported in major secure protocols. Organizations don’t need to wait for further developments to implement these protections.
Third, plan ahead for digital signature migration, especially for enterprises managing their own public key infrastructure. Large organizations with complex systems and long upgrade cycles must start early to ensure cryptographic agility.
“Quantum threats aren’t a hypothetical future concern – they represent an actionable risk today,” emphasizes Brian LaMacchia, Distinguished Engineer at Microsoft Research. “Organizations that delay implementing quantum-safe measures are effectively gambling with their most sensitive data.”
As quantum computing advances accelerate, the window for proactive protection narrows. The choice is clear: implement PQC defenses now or potentially face devastating consequences when quantum decryption capabilities arrive. For forward-thinking security leaders, the path forward involves embracing post-quantum cryptography as an essential component of their security posture.
Fact Checker
Verify the accuracy of this article using The Disinformation Commission analysis and real-time sources.



19 Comments
Quantum computing’s ability to break current encryption is a wake-up call for the cybersecurity community. Implementing post-quantum cryptography is crucial to safeguarding sensitive data and preventing catastrophic breaches down the line.
Absolutely. The financial, reputational, and legal consequences of these breaches can be severe, regardless of when they occur. Proactive measures are essential.
The quantum threat to cybersecurity is clearly a real and pressing issue that deserves urgent attention. Enterprises must act now to implement post-quantum cryptography and safeguard their data and communications against this looming threat.
Absolutely. Cybersecurity experts are sounding the alarm for good reason. Dismissing these concerns would be a grave mistake with potentially catastrophic consequences. Proactive measures are essential.
The ‘harvest now, decrypt later’ strategy used by malicious actors is a chilling reminder of the urgency of this issue. Enterprises can’t afford to be complacent about the quantum threat. Post-quantum cryptography deployment is essential to safeguarding the future.
It’s worrying to hear that many enterprises remain hesitant to implement post-quantum cryptography. This technology is essential to protect against the looming threat of quantum computing. Misinformation and complacency can’t be allowed to undermine cybersecurity efforts.
I share your concern. The gravity of this threat requires immediate action from organizations to safeguard their sensitive data and communications.
This is a serious issue that deserves attention. Quantum computing poses a real threat to cybersecurity, and organizations need to be proactive in adopting post-quantum cryptography to protect sensitive data. Dismissing these concerns as ‘distant doomsday thinking’ is shortsighted.
I agree. The ‘harvest now, decrypt later’ strategy used by malicious actors is especially concerning. Organizations can’t afford to be complacent about this threat.
Cybersecurity is a critical issue that affects us all. Misinformation and complacency around the quantum threat can have devastating consequences. I hope this article encourages more enterprises to prioritize post-quantum cryptography and strengthen their defenses.
The ‘Q day’ timeline of 2030 is sooner than many might expect. Malicious actors are already exploiting this vulnerability by stockpiling encrypted data. Enterprises need to take the quantum threat seriously and prioritize post-quantum cryptography deployment.
Agreed. The ‘harvest now, decrypt later’ strategy is especially alarming and highlights the urgency of this issue. Cybersecurity experts’ warnings should not be ignored.
This article highlights the critical importance of addressing the quantum threat to cybersecurity. Enterprises need to take this issue seriously and prioritize the deployment of post-quantum cryptography to protect their sensitive data and communications.
I agree. Misinformation and complacency can’t be allowed to undermine these essential cybersecurity efforts. The stakes are too high, and the consequences too severe to ignore.
This is a concerning development in the world of cybersecurity. The potential for quantum computers to break current encryption is a serious threat that organizations need to address proactively. Implementing post-quantum cryptography should be a top priority.
I agree completely. The financial, reputational, and legal risks associated with these breaches are simply too high to ignore. Decisive action is required to protect sensitive data and communications.
This article highlights the critical importance of addressing the quantum threat to cybersecurity. Enterprises need to take this issue seriously and prioritize the deployment of post-quantum cryptography to protect their sensitive data and communications.
Quantum computing’s ability to break current encryption is a sobering reality. Cybersecurity experts are right to sound the alarm and urge organizations to implement post-quantum cryptography. Dismissing these concerns as ‘distant doomsday thinking’ is short-sighted and dangerous.
Absolutely. The potential for catastrophic data breaches, regardless of when they occur, is simply too high a risk to ignore. Proactive measures to strengthen cybersecurity defenses are crucial.