Listen to the article
Iranian Cyber Threats Escalate as Hackers Expand Targets to U.S. Infrastructure
Pro-Iranian hackers have intensified their cyberattacks beyond the Middle East into United States territory, security experts warn. This digital offensive poses growing risks to American defense contractors, power stations, and water treatment plants as they become potential targets in an expanding wave of cyber chaos that could worsen if Tehran’s allies join the conflict.
In a significant development this week, hackers supporting Iran claimed responsibility for a major cyberattack against Michigan-based medical device company Stryker. The group, known as Handala, stated the attack was retaliation for suspected U.S. strikes that allegedly killed Iranian schoolchildren.
“What distinguishes this group is its clear focus on data destruction rather than financial extortion,” explained Ismael Valenzuela, vice president of threat intelligence at cybersecurity company Arctic Wolf.
Since hostilities escalated on February 28, pro-Iranian hackers have attempted to penetrate surveillance cameras in Middle Eastern countries to improve Iran’s missile targeting capabilities. They’ve also targeted data centers in the region, industrial facilities in Israel, a school in Saudi Arabia, and an airport in Kuwait.
The hackers openly discuss their strategic intentions on platforms like Telegram. “The datacenters need to be taken out,” wrote one user in a message uncovered by researchers at U.S.-based SITE Intelligence Group. “They host the brains of USA’s military communication and targeting systems.”
Iran has invested heavily in developing its offensive cyber capabilities while cultivating relationships with various hacking groups. In recent years, groups working at Tehran’s direction have infiltrated President Trump’s campaign email system, targeted U.S. water treatment plants, and attempted to breach networks used by the American military and defense contractors.
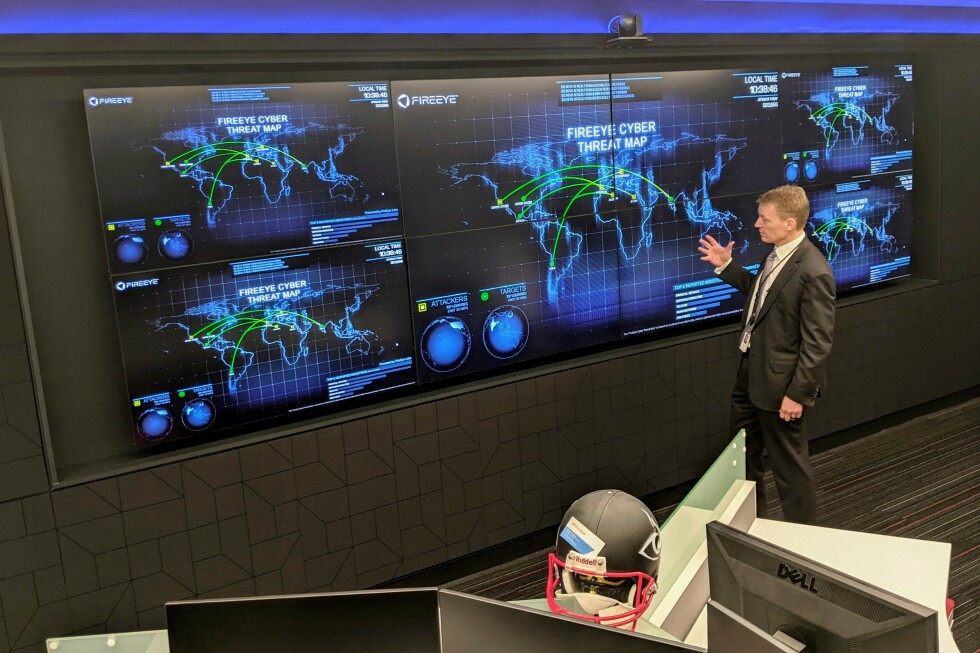
“Something is going to happen because the gloves are off,” warned Kevin Mandia, founder of the cybersecurity companies Mandiant and Armadin.
Security analysts believe U.S. defense contractors, government vendors, and businesses with ties to Israel are likely future targets. Critical infrastructure including hospitals, ports, water plants, power stations, and railways are also considered vulnerable. Polish authorities are currently investigating a cyberattack on a nuclear research facility that may have Iranian connections, though they acknowledge the possibility that another group could be using the Iran conflict as cover.
The recent military strikes on Iran and internet disruptions within the country may have temporarily limited Tehran’s cyber operations. However, experts believe Iranian hackers and their allies will pursue quick victories by targeting the most vulnerable elements of American cybersecurity infrastructure.
Local water treatment facilities and healthcare providers often lack resources for adequate cybersecurity, making them favored targets due to both their vulnerability and the potential public panic their disruption can cause. Common attack methods include denial-of-service attacks that jam networks, website defacements, and hack-and-leak operations threatening to release sensitive stolen information.
“Patch your systems. Ensure your firewalls and security solutions are up to date,” advised Shaun Williams, a former FBI and CIA officer now working as a senior director at cybersecurity firm SentinelOne. “Remove your stale accounts. All the cyber hygiene that you should be doing, it’s more critical now than ever. Prepare for disruption.”
While Russia and China are considered the greatest cyber threats to the U.S., with North Korea representing a growing concern, Iran has compensated for its more limited resources with innovative approaches. Tehran’s digital operatives have impersonated American activists online to covertly encourage anti-Israel protests on college campuses and established fake news websites primed to spread misinformation during U.S. elections.
The escalating threat prompted the Department of Homeland Security to issue a public warning about Iranian cyber threats last year.
“Iran and especially the proxies don’t care how big or smart you are. This is about making an impact, about creating chaos,” explained James Turgal, a cybersecurity expert and former FBI agent who now serves as a vice president at Optiv.
Security researchers are closely monitoring whether Russia, China, or allied hacking groups might provide support to Iran’s cyber operations. There’s already evidence of pro-Iranian hackers in Russia taking action, with researchers at cybersecurity firm CrowdStrike detecting increased activity from Russian hackers supporting Tehran since the conflict began.
One group known as Z-Pentest has claimed responsibility for disrupting several U.S. networks, including systems controlling closed-circuit video cameras. According to Adam Meyers, head of counter adversary operations at CrowdStrike, “Western organizations should continue to remain on high-alert.”
Fact Checker
Verify the accuracy of this article using The Disinformation Commission analysis and real-time sources.



8 Comments
The attack on the medical device company is a new front in this cyber conflict. Targeting civilian infrastructure like that is deeply concerning. Cybersecurity needs to be a top priority to defend against these kinds of disruptive attacks.
I’m curious to know more about the group Handala and their motivations. Retaliation for alleged strikes on Iranian schoolchildren is a serious accusation. Transparency and accountability around these cyber activities will be crucial.
Good point. Understanding the groups behind these attacks and their grievances is important context. Escalating tit-for-tat cyber strikes could quickly spiral out of control.
Interesting that the hackers are now focusing on surveillance camera data to improve missile targeting. This suggests a troubling military dimension to their cyber activities. The potential for escalation and retaliation is concerning.
Definitely a concerning development. Protecting critical infrastructure and military assets from these types of cyber threats will be a major challenge going forward.
Concerning to hear about the escalation of Iranian cyber threats targeting critical U.S. infrastructure. Seems the hackers are shifting from financial extortion to more destructive data attacks. Vigilance is needed to protect against these emerging risks.
You’re right, the shift to data destruction is particularly worrying. Cybersecurity will be crucial to safeguard against these state-sponsored threats, especially as tensions rise.
The growing risks of cyberattacks during periods of geopolitical tension is really troubling. Protecting critical infrastructure and preventing further escalation should be top priorities for policymakers and cybersecurity experts.